What Does the VAPT Testing Process Look Like?
Step 1: Planning and Scoping
Planning and scoping involve defining the objectives, scope, and boundaries of the test. This phase ensures that all stakeholders have an understanding of what assets will be assessed and what methods will be employed. It allows for the identification of sensitive areas that need focused attention, aligning the testing strategy with organizational goals.
In addition to setting clear objectives, planning and scoping involve selecting the right tools and methodologies. This choice is crucial in ensuring that the test covers all necessary aspects with depth. Engaging with key stakeholders during this stage helps in gathering input on areas of concern and integrating these into the testing strategy.
Step 2: Information Gathering
Information gathering, or reconnaissance, is a phase where data about the target systems is collected to aid the subsequent stages of testing. This involves gathering technical details such as network structures, server configurations, and application platforms, among others. Information gathering broadens the tester’s understanding of potential entry points and weaknesses, laying the groundwork for both vulnerability assessment and penetration testing.
The collected data acts as a roadmap to identifying known vulnerabilities and exploitable weaknesses in the system. This phase uses both active and passive techniques, with active methods directly interacting with the target system, while passive techniques gather information through publicly available sources.
Step 3: Vulnerability Assessment
Vulnerability assessment is the process of identifying and classifying security holes in the system. This step utilizes automated tools together with manual techniques to scan and evaluate the network and application environments for vulnerabilities. The goal is to provide a prioritized list of identified risks based on severity.
Once vulnerabilities are identified, they are presented in structured reports that detail their potential impact, along with recommendations for remediation. The assessment’s findings assist in forming a foundation for crafting defense strategies tailored to the unique needs of the organization.
Step 4: Penetration Testing
Penetration testing explores the vulnerabilities identified in the previous steps, actively simulating attacks to determine potential impacts. This hands-on testing involves using both automated tools and manual techniques to exploit security weaknesses, examining how a potential attacker could breach systems.
Through this controlled exposure, organizations can understand the real-world effectiveness of their security measures and incident response protocols. The penetration testing results provide insights into the practical implications of vulnerabilities, allowing stakeholders to see the potential damage these flaws could cause. This helps refine defensive strategies and fortify systems.
Step 5: Reporting and Remediation
The reporting phase compiles all findings from the VAPT process into a document outlining vulnerabilities, their severity, and remediation steps. This report serves as an instrument for decision-makers, enabling them to prioritize actions based on detailed risk assessments. Recommendations the report provides guide organizations towards remediation strategies tailored to their risk profiles.
Successful remediation follows a structured approach using the insights from the vulnerability and penetration reports. This step involves deploying security patches, reconfiguring systems, and implementing improved monitoring measures. By addressing identified vulnerabilities through remediation, organizations can strengthen their security posture.
Step 6: Rescan and VAPT Certificate Issuance
Once vulnerabilities have been addressed, rescanning evaluates the effectiveness of the remediation efforts, ensuring that previously identified weaknesses have been resolved. This step verifies the closure of vulnerabilities and ensures organizational systems have been appropriately remediated.
The rescan serves as a final quality check, readying the system for certification. Issuance of a VAPT certificate following a successful rescan demonstrates compliance with security standards and best practices. It provides validation that the organization has undertaken rigorous security assessment and has mitigated identified risks, offering proof of a strong security posture.
5 Best Practices for an Effective VAPT Program
Organizations should consider the following practices when implementing a structured vulnerability assessment and penetration testing strategy.
1. Maintain an Updated Asset Inventory
Maintaining an updated asset inventory involves keeping a detailed account of all hardware, software, and network components within an organization. This ensures visibility of all assets that could be exploited by cyber threats. Accurate asset inventory is the cornerstone of any security assessment, providing a picture of what needs to be tested and protected in the VAPT process.
An up-to-date asset inventory simplifies the vulnerability management process, enabling efficient identification of affected systems during testing. This practice supports security planning and threat mitigation by ensuring that all potential entry points are secured.
2. Utilize a Combination of Testing Methods
Combining different testing methods in VAPT ensures coverage of vulnerabilities. Using both automated and manual testing approaches provides a balanced evaluation, where automated tools efficiently identify common flaws, and manual techniques uncover intricate and context-specific vulnerabilities.
The integration of varied testing methodologies improves validation of vulnerabilities, reducing false positives. It also allows organizations to identify a wider array of vulnerabilities and address them with precision. Automated tools' efficiency and manual testing's adaptability provide a well-rounded perspective of a system's security status. Organizations benefit by having a nuanced understanding of their vulnerabilities.
3. Conduct Tests in a Controlled Environment
Conducting tests in a controlled environment is essential to limit potential disruptions during the VAPT process. This involves setting predefined conditions that enable testing without risking production environments' integrity. Controlled environments mimic real-world systems while isolating testing actions to prevent unintended impacts on business operations and sensitive data. Such an approach ensures that security assessments are both safe and accurate.
Using development or staging environments for testing identifies issues without risking production downtime. This practice forms a safety net for organizations, ensuring that security improvements do not interfere with system availability or data integrity.
4. Collaborate with Development and Operations Teams
Collaboration with development and operations teams throughout the VAPT process improves the effectiveness of testing efforts. These teams provide insights into the system architecture, application logic, and operational workflows, helping testers tailor their methods accordingly. Regular communication and collaboration foster a shared understanding of security challenges and the necessary steps to address them.
By collaborating with these key stakeholders, organizations ensure that identified vulnerabilities are addressed efficiently and sustainably. Development and operations input is critical in evaluating the feasibility of remediation strategies and implementing them without disrupting ongoing activities.
5. Implement Continuous Monitoring and Regular Testing
Implementing continuous monitoring and regular testing is vital for maintaining an effective security posture over time. Continuous monitoring identifies new threats and changes before they escalate into significant risks, supporting timely response actions. Regular testing ensures that any security measures in place remain effective against evolving threat landscapes.
Routine assessments help in validating the efficacy of implemented security controls and uncovering new vulnerabilities as systems evolve. This ensures that organizations adapt to changes and remain resilient in the face of emerging threats.
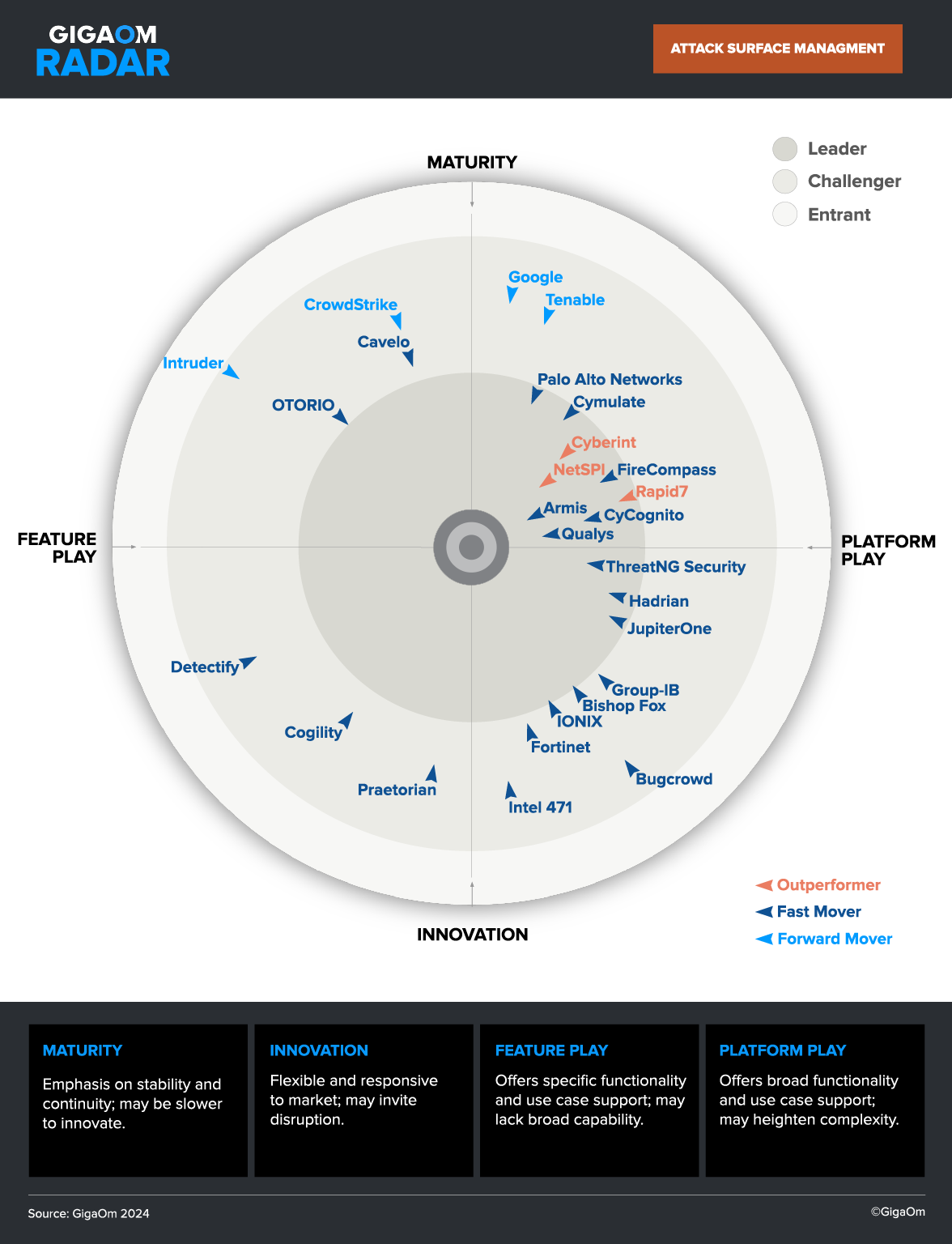
Vulnerability Management with CyCognito External Attack Surface Management
The CyCognito platform addresses today’s vulnerability management requirements, built on the foundation of full discovery of your entire extended IT ecosystem, to help you proactively defend against threats from even the most sophisticated attackers. It operates continuously and autonomously using advanced attacker-reconnaissance techniques to identify attackers' paths of least resistance into your environment so that you can efficiently eliminate them.
Once it identifies potential attack vectors, it prioritizes risks and delivers both actionable remediation guidance and ongoing validation of fixes. The result is a platform that delivers risk-based vulnerability management for your entire attacker-exposed IT ecosystem, closing what is a significant gap in existing attack surface management and vulnerability management processes.
The CyCognito platform uniquely delivers:
- Full discovery of your extended IT ecosystem, including assets that are part of your IT ecosystem, but are unknown or unmanaged by you.
- Sophisticated discovery capabilities that go beyond typical attack surface management or VM tools, which rely on passive data collection within known IP ranges.
- Detection and testing of attack vectors across your entire attacker-exposed IT ecosystem, going well beyond CVEs to include data exposures, misconfigurations and even software zero-day vulnerabilities.
- Prioritization of the attack vectors in your IT ecosystem based on what could impact your organization most from a cybersecurity risk perspective.
- Actionable remediation guidance and reporting to accelerate your remediation and validation.
Learn more about the CyCognito platform.



 Complimentary Report
Complimentary Report