Product Manager at CyCognito
March 3, 2025
Managing cybersecurity with constantly changing IP addresses can feel like chasing a moving target. Dynamic IPs, such as from content delivery networks and load balancers, create security blind spots and reduce asset visibility. Without appropriate context and history, security teams waste time on noise while real threats go unnoticed. This blog explores the challenges of dynamic IPs and how CyCognito helps organizations cut through the clutter for clear, actionable security insights.

Chief Marketing Officer
November 18, 2024
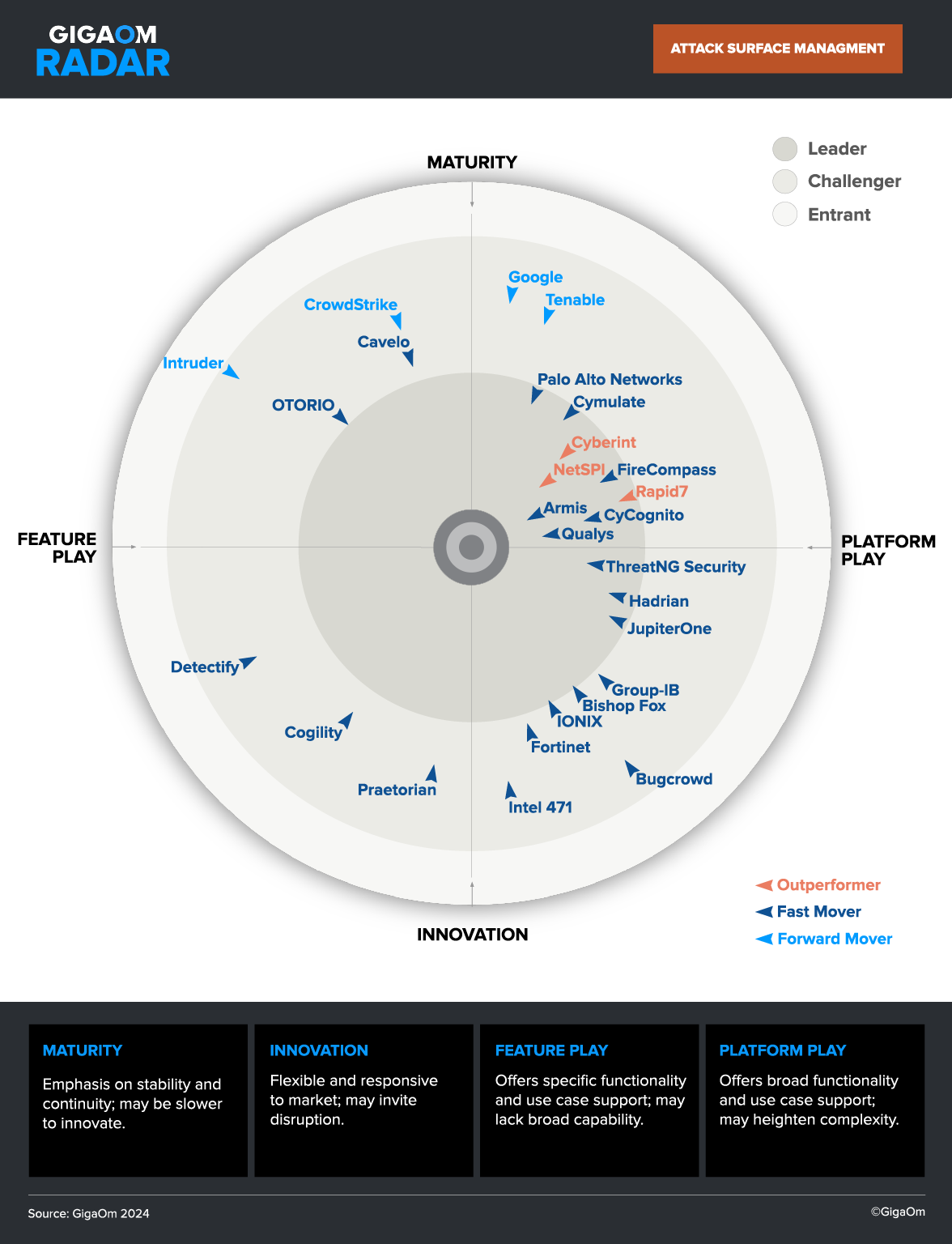
External Attack Surface Management (EASM) is crucial for reducing risks associated with unknown and unmanaged digital assets, which are responsible for over 65% of breaches. This post provides practical guidance on budgeting for EASM, including cost ranges, staffing requirements, and justifications based on risk reduction, labor savings, and operational efficiencies. Learn how EASM can optimize your security investments while improving your organization’s overall cybersecurity posture.

Customer Marketing and Advocacy Lead
July 22, 2024
I recently sat down with Daniel Schlegel, the Global Chief Information Officer (CIO), Chief Security Officer, and Chief Privacy Officer of Berlitz Corporation, a global leader in language training and cultural education, to hear about their transformative experience using CyCognito to gain global external attack surface visibility, reduce costs, and enhance their security posture.

Product Marketing Manager
November 21, 2023
Cyber Monday is right around the corner and millions of consumers will flock to ecommerce websites in search of the best deals. But can shoppers be assured that the sites they do business with are secure and compliant? Before and during the holiday shopping season, retailers need to ensure that ecommerce websites with missing WAFs, cryptographic vulnerabilities, or easily exploited critical issues.

Product Marketing Manager
November 13, 2023
Generative AI is a form of artificial intelligence that generates new content –including text, images, and video – in response to user prompts. These AI models are trained on huge volumes of data and use algorithms to create content that has a similar structure to their training data

Was a Product Manager at CyCognito
September 29, 2023
Web Application Firewalls (WAFs) are the most common protection for web applications. WAFs protect web applications by filtering and monitoring HTTP traffic between the application and the internet. However, WAFs need to be deployed and configured to protect web applications specifically. If they are not, this leaves open a potential route for an attacker.

Product Marketing Manager
September 6, 2023
Have you ever wondered just how much the average external attack surface changes every month?

Was a Senior Product Marketing Manager at CyCognito
August 24, 2023
Vulnerability prioritization is the process of identifying and ranking vulnerabilities in order to focus efforts on the most important vulnerabilities.

Chief Marketing Officer
August 3, 2023
Manage the entire attack surface with external exposure management. Learn more about the key ways to safeguard your attack surface at CyCognito.

Sr. Technical Marketing Manager
March 16, 2023
Solving meaningful external risk challenges requires the right information at the right time in the hands of the right people.