Solutions
Technical Use Cases
EASM
AutoPT
CAASM
UVM
CNAPP
AppSec
Business Use Cases
Assess Your Security Effectiveness
Evaluate Merger & Acquisition Risk
Monitor Subsidiary Risk
Prioritize & Eliminate Attack Vectors
Secure Your Software Supply Chain
Simplify Compliance Initiatives
Industry Solutions
Manufacturing
Resources
What's New
Research Reports
White Papers + eBooks
Solution Briefs
Datasheets
Webinars
Videos
Learning Center
API Security
Application Security
Attack Surface
Cloud Security
Cyber Attack
DRPS
Exposure Management
Penetration Testing
Vulnerability Assessment
Vulnerability Management
EASM 101
External Attack Surface Management
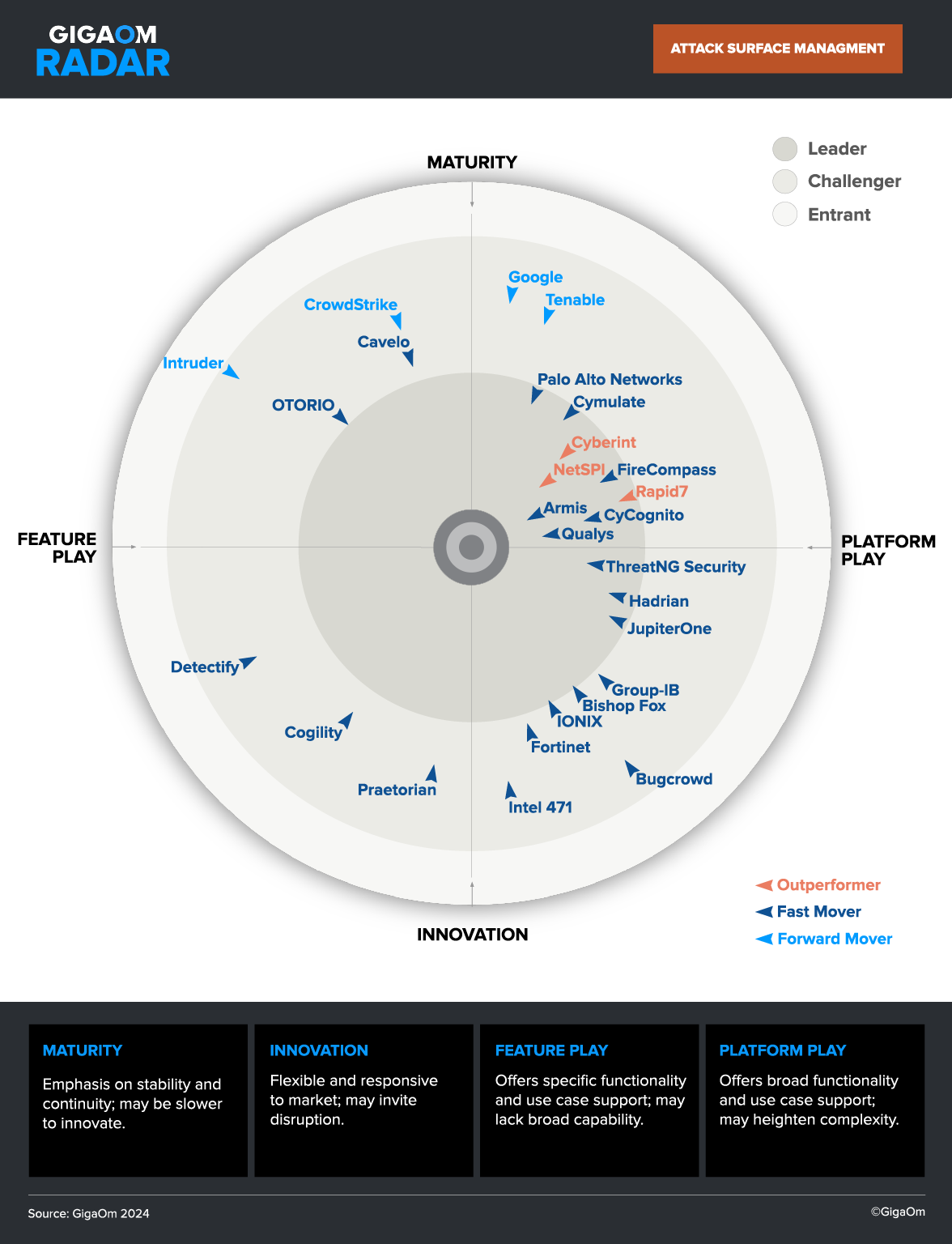
Attack Surface Management
Attack Surface Discovery
Attack Surface Protection
Attack Surface Reduction
Security & Compliance
Glossary
Blog
Emerging Threats