Security teams are under constant pressure to improve, but they often struggle. Like pushing a square wheel instead of taking the time to install a round one, organizations are often caught running the same plays because transformation is disruptive. There is never the right time for sweeping change, which just builds frustration due to delays, siloed teams and manual workflows.
Gartner’s 2022 release of Continuous Threat Exposure Management (CTEM) is a response to a need to evolve from the traditional workflows that have been the norm for decades. CTEM is a program that relies on people, processes and technology to be successful. Cyber security leaders frustrated with the status quo and looking for the right model to align with should explore CTEM for fit. If implemented properly, the program can enable a significant reduction in mean time to detect (MTTD), analysis time and mean time to remediation (MTTR) of threats.
What is Continuous Threat Exposure Management (CTEM)?
CTEM is a coordinated threat response process that focuses on proactive risk and vulnerability detection, rapid communication and validated response. Communication involves not only the right people, but also the right information to make informed decisions. This shift from reactive to proactive not only prevents attacks from being successful, but also ensures cross-functional teams are aware and have input on the solution.
Recent research1 validates this need. Eighty-one percent of respondents say improving collaboration between teams is important to improving risk identification and prioritization workflows, yet only 22% of respondents’ organizations have a cross-functional team assigning priority for remediation.
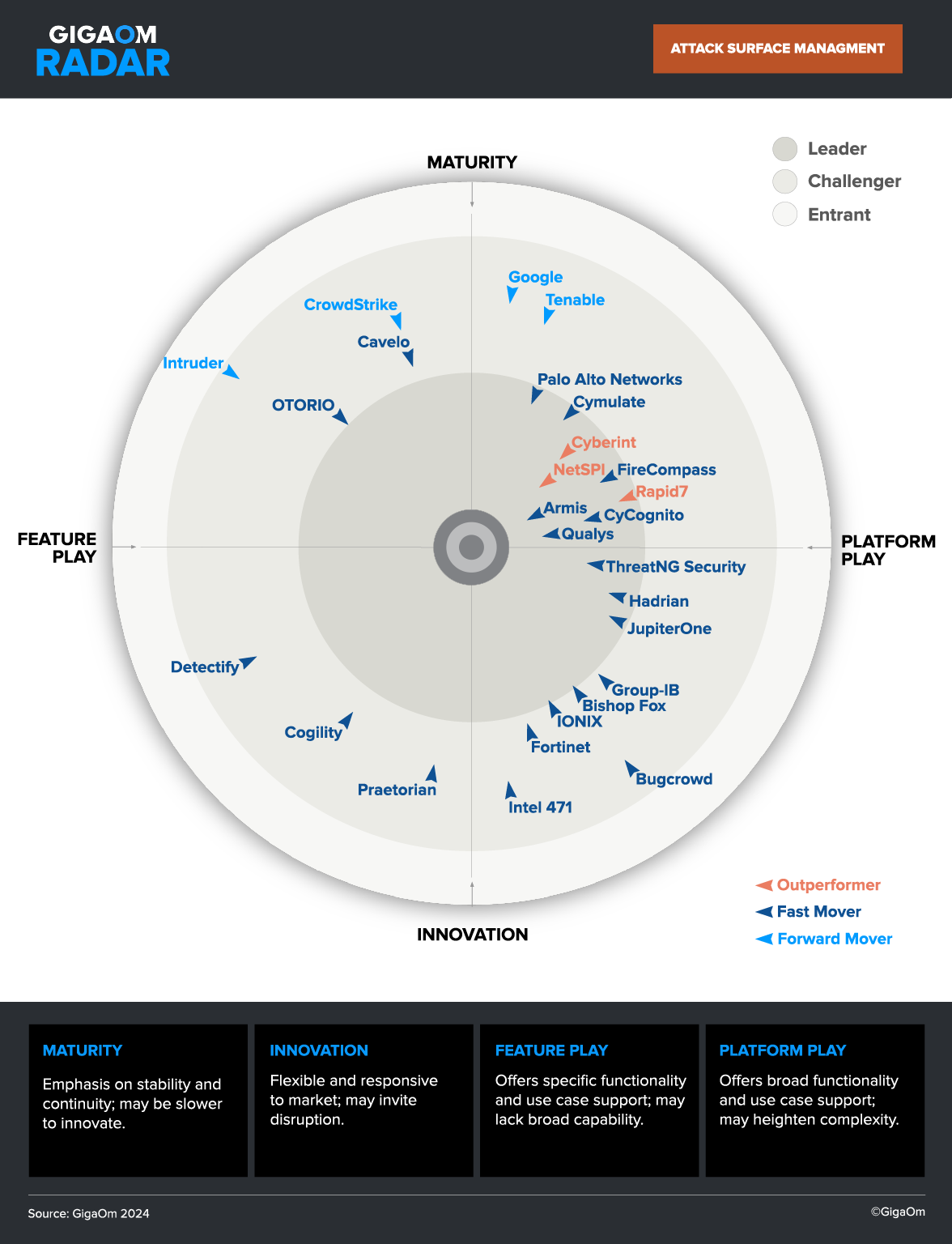
Complexity is the enemy of any security program. As a result, choosing the right technology for external exposure management is critical to success.
External Assets (and Exposures) Have Unique Challenges
CTEM involves all exposures, both internal and external. Most front line remediation teams know that externally exposed assets have their own risk management challenges and that these challenges cannot be met at scale using manual workflows and legacy security technologies. These challenges include:
- The external attack surface changes too rapidly – Up to 10% per month2
- The external attack surface is too big – Unknown infrastructure segments that can contain thousands of assets
- Vulnerability scans don’t identify all risk – Passive scanning based CVEs alone are superficial but adding active testing increases complexity exponentially
- Scan cadence doesn’t maintain pace with risk – Monthly/quarterly scans can’t keep up
- Too many issues to patch – Lack of accurate severity scores mean too many issues are critical or high
Most teams respond with “If we just work faster we will get it done”. More frequent scans, more people tracking change, more prioritization and status meetings. Unfortunately this isn’t a scalable answer. Automation and a modern approach is the only path forward.
Moving from Chaos to Coordination
Even the most mature security team can have elements of chaos. Manual workflows, asset inventory spreadsheets, infrequent updates, incomplete email distribution lists, status update meetings and emergency maintenance windows leave behind a feeling of instability.
Adopting CTEM is a journey. Changing behaviors and processes can be difficult, but technology doesn’t have to be. The key is to define the goal and then break it down into smaller pieces. Some examples:
- People. What representatives from each business unit are associated with risk? Ensure these teams have input to the new goal (and ensure their management buys in on it too).
- Process. What is the current frequency of threat detection across all digital assets? How is this information shared? Identify gaps and work from there. Build team alias based email distribution lists – not person – and test them frequently.
- Technology. How many tools are in place both internally and externally? How many resources are assigned to manage this tooling? External threats to infrastructure are most common and pose significant risk; ensure risk to your external attack surface is identified promptly with automated tooling.
These are just some examples of questions to ask as you build your plan for CTEM adoption.
Shortcut CTEM Technology Selection with a Checklist
Evaluating technologies for CTEM adoption involves consideration of many capabilities. Each phase of CTEM has requirements that need to be met.
Download the CyCognito solution brief “Demystifying Continuous Threat Exposure Management” to shorten your ramp up on CTEM with definitions, requirements and a technology purchase checklist.
Our white paper “Understanding Continuous Threat Exposure Management” is a snapshot view into people, processes and technologies impacted by a CTEM deployment, as well as how CyCognito maps to CTEM requirements.
Find Out More About CyCognito’s Threat Exposure Management Solutions
CyCognito is a cloud-native software-as-a-service that was built to meet the external risk requirements of the largest and most complex organizations.
For more information on how CTEM maps to EASM and how CyCognito uniquely solves external risk management challenges, please visit cycognito.com.
1. Source: Forrester Research “Teamwork shines a light on hidden risk”, 2022
2. Source: CyCognito “State of External Exposure Management Report“, Summer 2023
Jason Pappalexis has worked professionally in cybersecurity for over 18 years in roles that include security administration for the US government, 3rd party testing, solutions architecture, product management, and technical product marketing.





 Attack Surface
Attack Surface