Sr. Technical Marketing Manager
October 14, 2024
Exposure Management (EM), introduced by Gartner in 2022, represents the evolution or vulnerability management. With EM, security teams can address visibility and testing gaps, and stay ahead of threats. This blog includes six signs that your organization needs EM, and five essential requirements to implement it.

Chief Marketing Officer
October 7, 2024
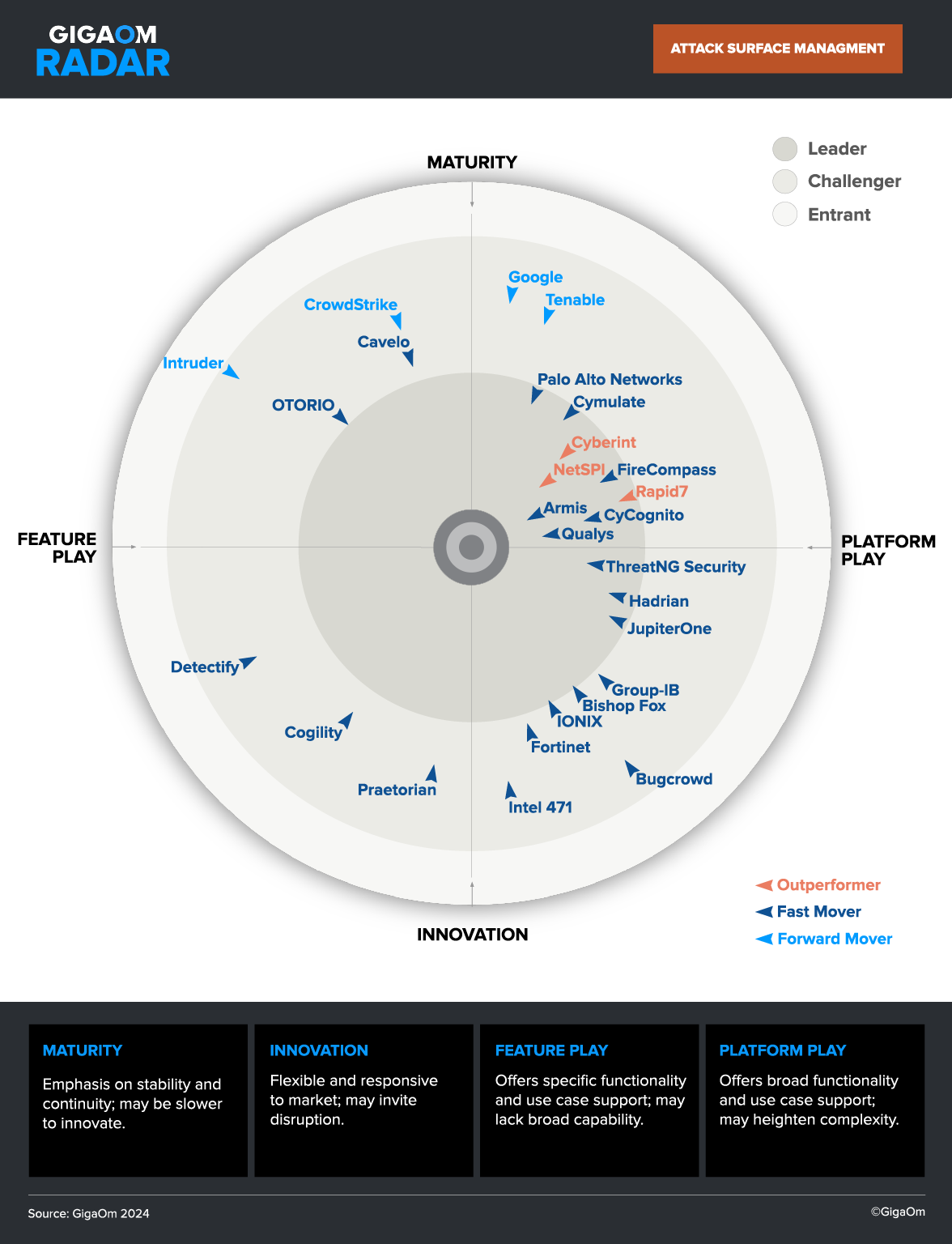
With EASM becoming essential to security operations, many vendors are jumping on board, but not all solutions are enterprise-grade. Basic EASM products can waste time, undermine security teams, and offer a false sense of protection. To avoid these pitfalls, ask your vendor these five critical questions—if they can’t answer, it’s a red flag.

Sr. Technical Marketing Manager
September 30, 2024
Many organizations believe their security testing is robust, but common tools like vulnerability scanning and penetration testing often leave surprising gaps. Infrequent tests, limited asset coverage and inaccurate results leave exposure and risk. Achieving ideal security goals requires full coverage, high accuracy, and frequent testing—criteria most approaches struggle to deliver. CyCognito bridges these gaps with automated testing for network systems and web applications, helping organizations strengthen their security, continuously.

Customer Marketing and Advocacy Lead
July 22, 2024
I recently sat down with Daniel Schlegel, the Global Chief Information Officer (CIO), Chief Security Officer, and Chief Privacy Officer of Berlitz Corporation, a global leader in language training and cultural education, to hear about their transformative experience using CyCognito to gain global external attack surface visibility, reduce costs, and enhance their security posture.

Customer Marketing and Advocacy Lead
July 1, 2024
I recently sat down with Daniel Maier-Johnson, the Chief Information Security Officer (CISO), and Markus Diehm, Cybersecurity Analyst, with Asklepios Kliniken GmbH, Germany’s second-largest private healthcare provider, to hear about their experience using CyCognito to gain continuous monitoring, prioritize cyber risks, and safeguard patient information.

Chief Marketing Officer
May 6, 2024
The U.S. SEC recently adopted new cybersecurity disclosure rules. This post describes the new disclosure rules and the potential burdens being placed on CISOs.

Customer Marketing and Advocacy Lead
March 4, 2024
Benjamin Bachmann, VP of Group Information Security at Ströer, transformed the German media conglomerate’s security posture by implementing CyCognito.

Was Sr. Director of Product Marketing
February 26, 2024
CISA’s proactive approach to cybersecurity is highlighted, focusing on two directives: BOD 22-01, which mandates agencies to consult the “Known Exploited Vulnerabilities Catalog,” and BOD 23-01, aimed at improving agency asset visibility and vulnerability detection. These directives emphasize asset discovery and vulnerability enumeration as crucial activities for risk reduction. CyCognito’s platform aligns with these directives by automating discovery, contextualizing assets, and prioritizing vulnerabilities based on attacker perspective, enabling organizations to efficiently close gaps in their attack surface management.

Product Marketing Manager
November 13, 2023
Generative AI is a form of artificial intelligence that generates new content –including text, images, and video – in response to user prompts. These AI models are trained on huge volumes of data and use algorithms to create content that has a similar structure to their training data

Sr. Technical Marketing Manager
October 18, 2023
Continuous threat exposure management (CTEM) is a risk reduction strategy introduced by Gartner in 2021. Designed to significantly reduce mean time to remediation (MTTR), it relies on coordination of people, processes and technology. Choosing the right CTEM technology is critical to efficient implementation.