What are CVE-2024-47176, CVE-2024-47076, CVE-2024-47175, and CVE-2024-47177?
On September 26, 2024, four critical vulnerabilities, CVE-2024-47076, CVE-2024-47175, CVE-2024-47176, and CVE-2024-47177, were disclosed in the open-source printing system Common Unix Printing System (CUPS) and its components. Attackers can leverage the remote code execution (RCE) and input validation vulnerabilities as part of an attack chain. Once a fake printing device on a network-exposed system running CUPS is created, any print jobs processed on the fake devices can be used to remotely execute malicious code.
What assets are affected by these vulnerabilities?
The issues above affect four different CUPS components:
- CVE-2024-47176 affects cups-browsed version 2.0.1
- CVE-2024-47076 affects libcupsfilters versions 2.1b1 and below
- CVE-2024-47175 affects libbppd versions 2.1b1 and below
- CVE-2024-47177 affects cups-filters versions 2.0.1 and below
These assets are primarily found on GNU/Linux systems.
Are fixes available?
Patches are not currently available for these issues.
Are there any other actions to take?
To mitigate potential exploitation, administrators can block UDP traffic on port 631. Alternatively, if CUPS is no longer in use, removed the cups-browsed service using the commands
- systemctl stop cups-browsed
- systemctl disable cups-browsed
Are these issues being actively exploited?
As of October 14th, there are no reports of active exploitation of these vulnerabilities.
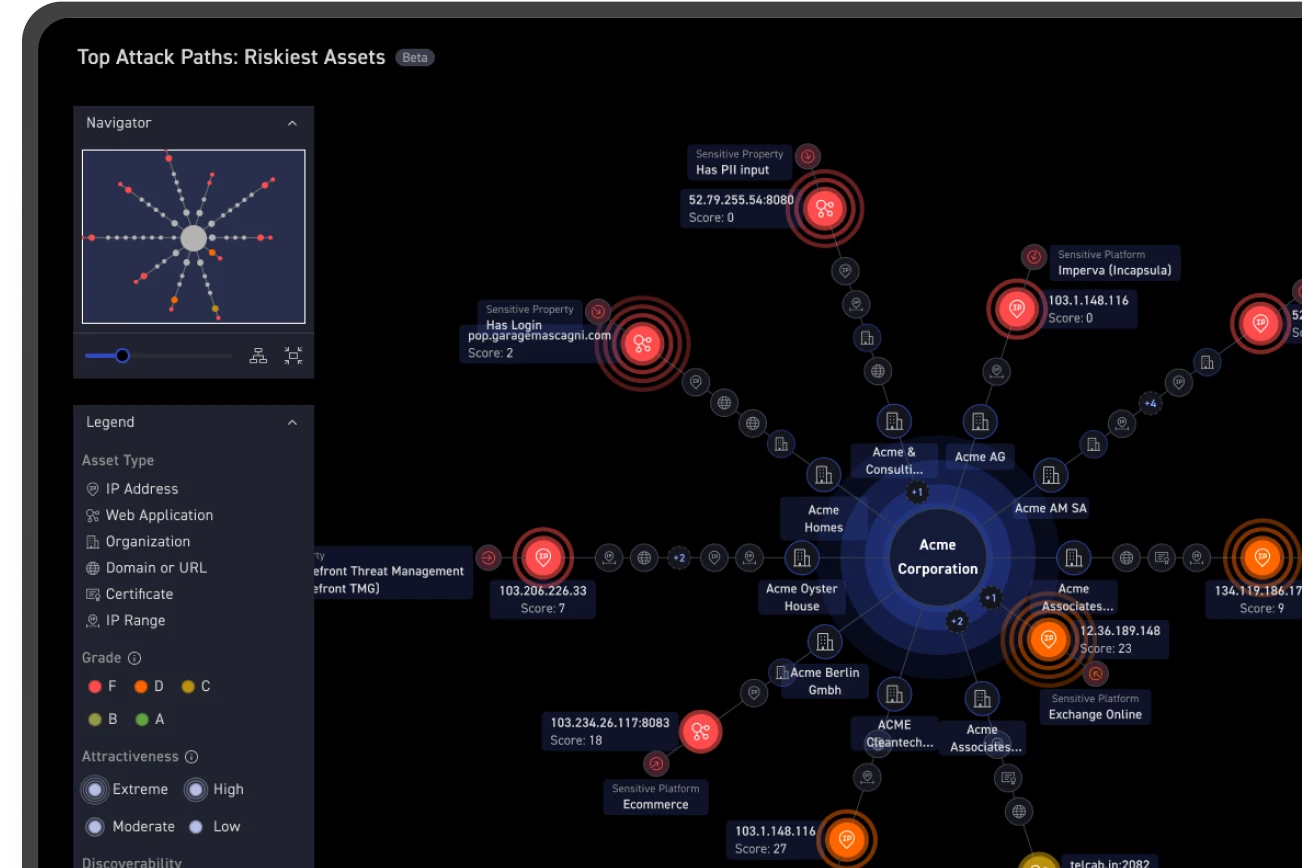
How is CyCognito helping customers identify assets vulnerable to these issues?
CyCognito is investigating active detection methods for these vulnerabilities. CyCognito users can check if any assets are running potentially vulnerable CUPS products using provided filters in the CyCognito platform. All customers have access to an in-platform emerging security issue announcement as of October 2nd, 2024.
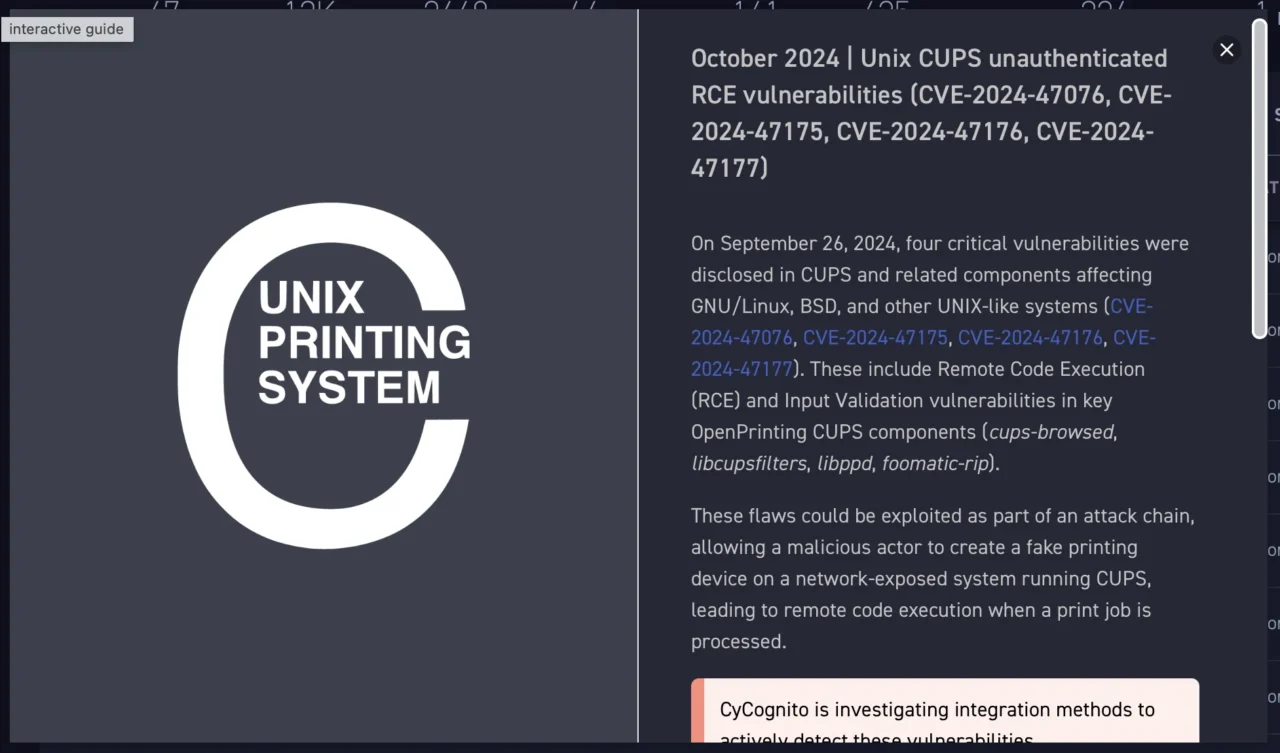
Figure 1: The alert sent by CyCognito for these issues.
How can CyCognito help your organization?
CyCognito is an exposure management platform that reduces risk by discovering, testing and prioritizing security issues. The platform scans billions of websites, cloud applications and APIs and uses advanced AI to identify the most critical risks and guide remediation. Emerging companies, government agencies and Fortune 500 organizations rely on CyCognito to secure and protect from growing threats. Want to see how it works? Check out our website and explore our platform with a self-guided, interactive dashboard product tour. To learn how CyCognito can help you understand your external attack surface and exposed risks, please visit our Contact Us page to schedule a demo.