The recent cyber intrusion campaign that leveraged modified SolarWinds software – now widely termed SUNBURST – has dramatically raised awareness of supply chain-based compromises and how intertwined organizations now are.
A Flanking Maneuver
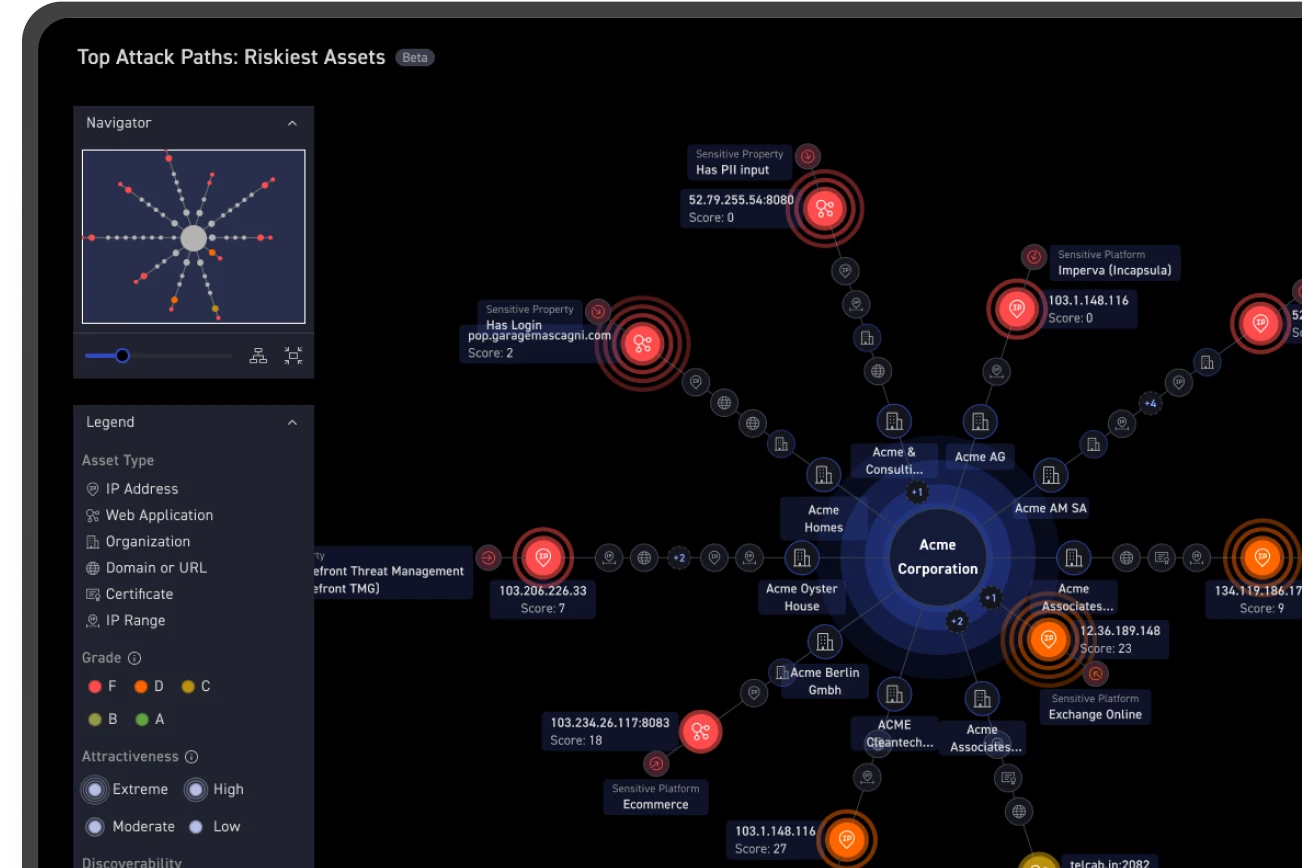
Supply chain attacks are rooted in the military concept of a “flanking maneuver” in which an offensive force attacks their opponent from the flank (i.e., side) rather than head-on where the bulk of defensive forces are focused. In the cyber world, attackers work the same, targeting those areas where you are least focused. Attackers go after the paths of least resistance, often starting in your business partners, IT suppliers, subsidiaries or other related organizations and leveraging any entity or digital asset that eventually gets them access to their ultimate target: your applications, data and networks.
Attackers understand that your IT ecosystem extends well beyond your own organization and that you don’t control the security of all of your supply chain participants. They also know that organizations don’t have an easy way to discover all of those IT assets and test them for potential attack vectors. The SUNBURST attacks demonstrate organizations can be blindsided by unseen security weaknesses and vulnerabilities they simply don’t know how to find, let alone resolve.
Research: Organizations Ignore Their Supply Chain
Most organizations focus almost entirely on protecting their known applications and infrastructure and that’s what virtually every cybersecurity tool is designed to do. No matter how large or small an organization’s security budget, very little spending is devoted to discovering, monitoring and protecting what is unknown.
The SUNBURST attacks make it clear that supply chain security is one of those unknowns. Research conducted by ESG and CyCognito confirms that: less than half of those surveyed consider partners and affiliates as extensions of their attack surface, and nearly half of organizations do not include SaaS applications and public cloud workloads in their definition of attack surface.